Content

The Security Wake-Up Call Every AI Team Needs
Most teams think about AI in terms of speed. Faster replies. Faster research. Faster execution. But the moment an AI agent gets access to your inbox, your customer data, your internal docs, or your financial tools, the conversation changes. It stops being just a productivity question and becomes a security question.
That shift still hasn’t clicked for enough business owners. I’ve had conversations where someone proudly shows me an AI setup that can touch email, CRM records, files, and operations from one shared agent. Then I ask a simple question: would you give every member of your team your banking password? The answer is always no. But functionally, that’s close to what many companies are doing when they deploy powerful agents with broad, poorly scoped access.
Why AI agents become dangerous so quickly
The paradox of AI agents is simple: the more useful they become, the more damage they can do when something goes wrong. A good agent is not just reading text. It is taking actions. It can send messages, move data, update records, trigger workflows, and make decisions at machine speed. That means every configuration mistake gets amplified.
A prompt injection is not just an odd edge case. A loop is not just a small bug. A confused permission model is not just technical debt. In an AI system, those issues can turn into operational incidents in minutes. The same automation that saves you ten hours a week can also create ten hours of cleanup before breakfast.
The mistake I keep seeing in real companies
The common pattern is not malicious. It’s convenience. People start with one helpful agent, then keep adding permissions because each new connection makes the system feel smarter. Soon that one agent can see everything, act everywhere, and operate on behalf of the entire company. It becomes a superuser by accident.
That is usually where the risk begins. Shared instances handling sensitive work create invisible fragility. One wrong prompt, one misunderstood instruction, one badly designed automation, and the system starts acting with the confidence of a trusted employee and the judgment of a machine that lacks context.
I’ve seen agents message customers repeatedly because of loop errors. I’ve seen automations send information to the wrong recipients. I’ve seen setups where any employee could unintentionally alter a core workflow simply by changing the wrong prompt or reconnecting the wrong tool. None of that feels dramatic while you are building it. It feels efficient. Until the day it doesn’t.
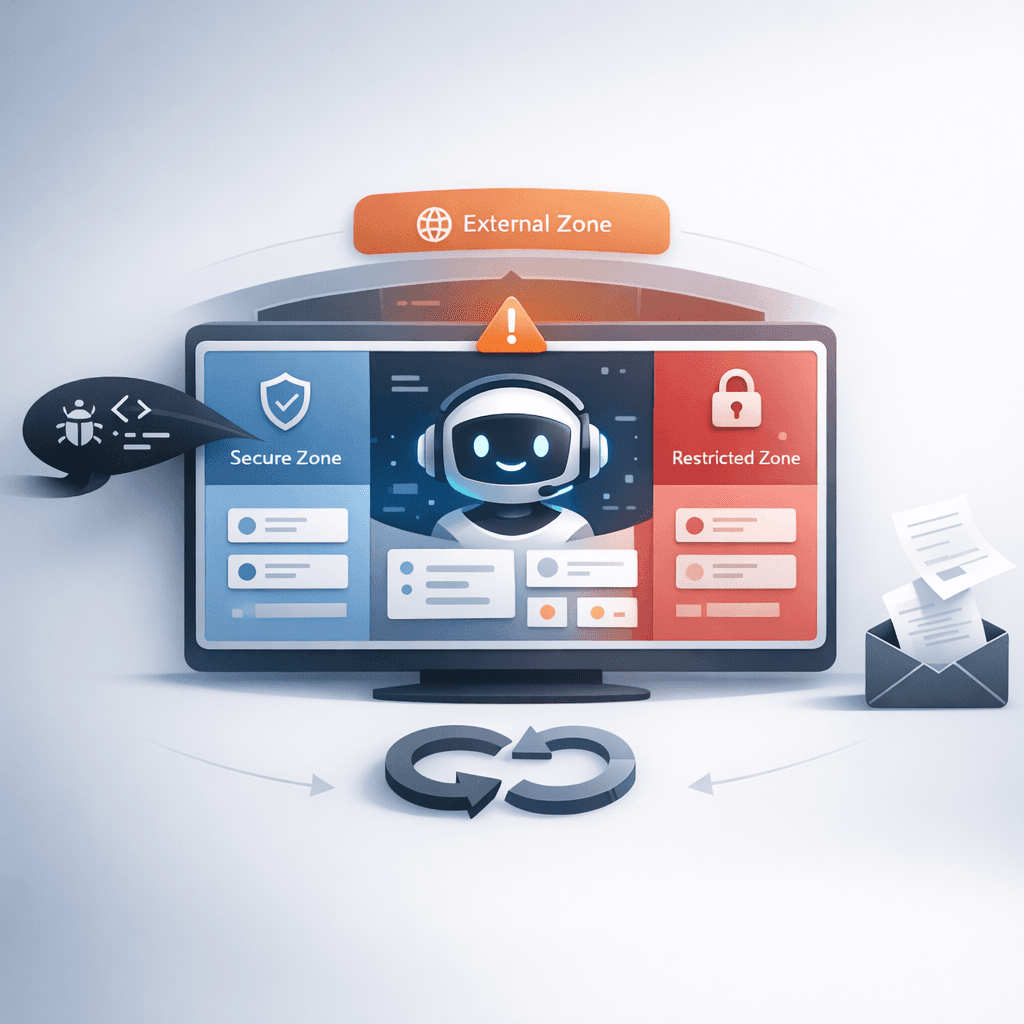
AI security is really about boundaries
The fix is not to avoid AI. The fix is to design your AI stack with the same maturity you would apply to money, credentials, and customer trust. Sensitive work should not live inside broad shared instances. Not every agent should have access to every system. Not every employee should operate through the same AI layer. Security starts with separation.
The safest setups I see are not the most complex ones. They are the clearest ones. One agent is allowed to draft internal content but not send external messages. Another can work on customer support but cannot touch billing. Another can summarize meetings but cannot access legal or financial information. Once you define boundaries, you make failure smaller. That is the real goal.
What business owners still underestimate
A lot of founders still treat AI security like friction. Something annoying. Something to solve later. But the uncomfortable truth is that security is what makes AI usable at scale. Without it, every new capability adds stress instead of leverage. You stop trusting the system. Your team hesitates to use it. And the tool that was supposed to reduce overhead becomes a source of anxiety.
When your automations are properly scoped, something important changes. You can finally relax. You are no longer wondering whether an agent will email the wrong person at 3 AM or expose something it should never have touched. You know what each system can access, what it can do, and where it must stop. That confidence is not a luxury. It is what makes delegation possible.
Productivity without control is not productivity
There is a version of the AI future where companies move fast, automate well, and still protect the integrity of their business. But that future does not come from plugging one giant agent into everything and hoping the prompts are good enough. It comes from architecture. From permissions. From guardrails. From deciding in advance what should remain separate.
I think that’s the part many people miss. Security is not the tax you pay for productivity. It is the condition that makes sustainable productivity possible. If your AI systems are going to handle meaningful work, they need meaningful boundaries. That is not paranoia. That is operational common sense.
The new standard companies need to adopt
We are entering a phase where AI agents will increasingly act as part of the company itself. They will write, answer, triage, move information, and execute processes. That means access design can no longer be an afterthought. Companies need to treat agent permissions the way they treat bank credentials, admin roles, and legal access. Principle of least privilege should become the default, not an advanced best practice.
The companies that understand this early will have a huge advantage. They will move faster because their systems are trustworthy. Their teams will adopt AI more confidently because the blast radius of mistakes is contained. And they will sleep better because automation is happening inside a structure designed to protect the business, not just accelerate it.
If you’re building with AI right now, this is the wake-up call: don’t just ask what your agents can do. Ask what they should never be allowed to do. That single question will save you more time, reputation, and pain than any growth hack ever will.


